How does NuCypher work?

The NuCypher network is a decentralized network of nodes that perform threshold cryptography operations serving users with secrets management and dynamic access control. nucypher is the python library and CLI for interacting with the decentralized threshold cryptography network.
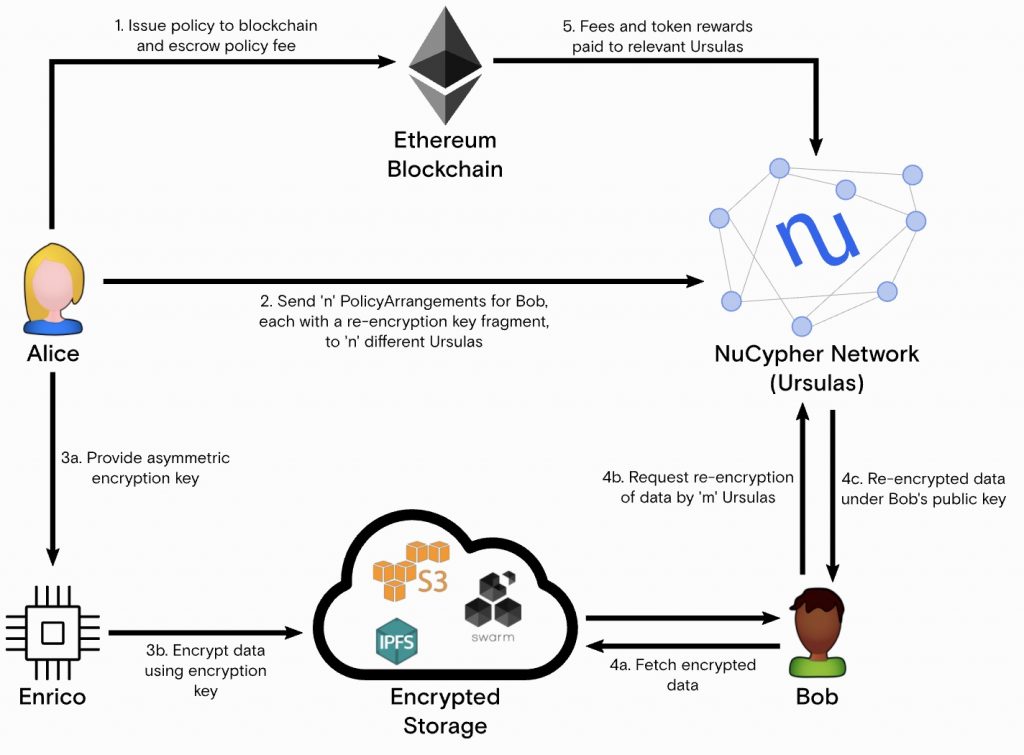
1. Alice, the data owner, grants access to her encrypted data to anyone she wants by creating a policy and uploading it to the NuCypher network.
2. A group of Ursulas, which are nodes on the NuCypher network, receive information about the policy, called a PolicyArrangement that include a re-encryption key share. The Ursulas stand ready to re-encrypt data in exchange for payment in fees and token rewards. Thanks to the use of proxy re-encryption, Ursulas and the storage layer never have access to Alice’s plaintext data.
3. Each policy created by Alice has an associated encryption key, which can be used by any entity (Enrico) to encrypt data on Alice’s behalf. This entity could be an IoT device in her car, a collaborator assigned the task of writing data to her policy, or even a third-party creating data that belongs to her – for example, a lab analyzing medical tests. The resulting encrypted data can be uploaded to IPFS, Swarm, S3, or any other storage layer.
4. Bob, a data recipient, obtains the encrypted data from the storage layer and sends an access request to the NuCypher network. If the policy is satisfied, the data is re-encrypted to his public key and he can decrypt it with his private key.
5. Ursulas earn fees and token rewards for performing re-encryption operations.
More detailed information:
Whitepapers
Network
https://github.com/nucypher/whitepaper/blob/master/whitepaper.pdf
“NuCypher – A proxy re-encryption network to empower privacy in decentralized systems” by Michael Egorov, David Nuñez, and MacLane Wilkison – NuCypher
Economics
“NuCypher Network: Staking Protocol & Economics” by Michael Egorov, MacLane Wilkison, Arjun Hassard – NuCypher
“NuCypher Network: Pricing Protocol & Economics” by Arjun Hassard – NuCypher
Cryptography
https://github.com/nucypher/umbral-doc/blob/master/umbral-doc.pdf
“Umbral A Threshold Proxy Re-Encryption Scheme” by David Nuñez – NuCypher
Staking
- Stakers and Workers
- Stake Initialization
- Stake Management
- Running a Worker
- Worker Diligence
- WorkLock
- Ibex Testnet
- Cloud Worker Management
Application Development
- Getting Started with Characters
- HTTP Character Control
- Alice & Bob CLI
- Local Development Fleet Testing
- Lynx Testnet
References
Demos
Architecture
- Character Concepts
- WorkLock
- Ethereum Contracts
- Approaches to Upgradeable Contracts
- NuCypher DAO
- Sub-stakes
- The Slashing Protocol
- Service Fees (Pricing)
APIS
Release Notes
Support